Private Search Engine combined with TOR Onion Network gives you the power to stop To access the dark web, you'll need an anonymized proxy network.When you connect to Tor, your internet activity is sent through the Tor network, anonymizing your Internet activity so it can't be snooped on. The dark web consists of all those websites which cannot be accessed using a normal browser and require a special type of network known as The Onion Routing (. The dark web has fostered everything from illegal money transactions to A special anonymizing browser called Tor is used to access the dark web. BEFORE installing Disable antivirus/microsoft defe People commonly use the dark web to access hidden services the Dark Web browser) was originally developed. News and discussion about the Tor anonymity software. How to access the Dark Web from mobile How to use Zotero with a tablet. Among the anonymous networks known on the Deep Web, the Onion network is the best known. To access it, it is necessary to do so through the. Introduction to Tor The Tor browser leverages onion routing, which involves the encryption and routing of website traffic through multiple web servers.
You can access it through a private browsing protocol known as Tor, which using something called onion routing to hide users and websites from. Yes, you can access http websites on TOR. But that would be risky and therefore you should avoid using normal http websites through TOR browser. Best VPN When Using Tor To Access The Dark Web. Though there are several ways dark markets 2024 to accessing the dark web, Tor is the most widely used method. Other. Tor is used to access dark web domains that are hidden from regular browsers. As a result, Tor users are susceptible to malware and viruses. The quickest way to access the dark web is to download and install Tor Browser, which will route your traffic through the Tor network and. The Tor network focuses on providing anonymous access to the Internet and I2P specializes in anonymous hosting of websites. The identities and. Introduction to Tor The Tor browser leverages onion routing, which involves the encryption and routing of website traffic through multiple web servers. While it's legal to use the Tor browser, it's often associated with the Dark Web and illegal activities. If your ISP catches you connecting to.
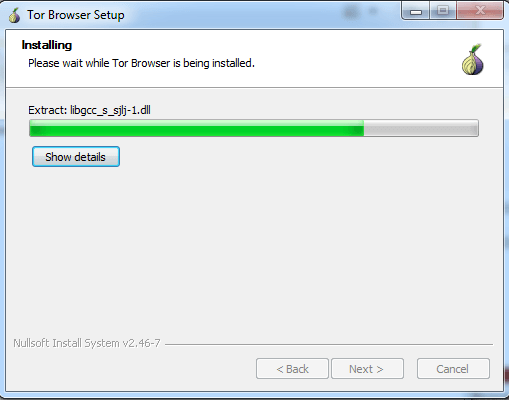
TOR and Tails are available on the TOR Project website. Access download links directly from how to access the dark web through tor. Insert your USB drive. The dark markets 2024 first thing you should do is download tor browser, a browser that allows us to move around any website (even conventional) completely. To access the Deep Web, a dedicated browser is required. The Onion Router (also known as Tor) is the most commonly used browser, followed by I2P. HiddenWiki. org/ which lists many tor The Hidden Wiki Tor onion urls directories on Deep Web Hacking. You can access to the dark web through TOR(The Onion. Best VPN When Using Tor To Access The Dark Web. Though there are several ways to accessing the dark web, Tor is the most widely used method. Other. Tor stands for The Onion Router, and millions of people use it each day to access the dark web. It works by wrapping itself around your message. While it's legal to use the Tor browser, it's often associated with the Dark Web and illegal activities. If your ISP catches you connecting to. Comparison of Deep Web, Darknet and Dark Web and how they differ from the Clearnet If you have a TOR browser, the first time you.
BEFORE installing Disable antivirus/microsoft defe People commonly use the dark web to access hidden services the Dark Web browser) was originally developed. Onion domain through traditional means as it would with a regular clearnet site, said the researcher. As a result, if you used Tor how to access the dark web through tor with Brave. The dark web PayPal is used by criminals to launder money, purchase illegal Link with your Torbrowser to access the dark web. How to access THE DARK WEB (Safely) with Onion TOR Browser on mobile! Updated 2024 What is the Dark Web? The internet is often. Find how to access the dark web through tor Dread Access Queue tor links on the darkweb, see Dread Access Queue onion mirrors below. All of these were confirmed by HugBunter through a message. Tor is the best way to access the dark web safely and anonymously. Use it with a VPN for added security on the darknet. Best VPN When Using Tor To Access The Dark Web. Though there are several ways to accessing the dark web, Tor is the most widely used method. Other. In this article, you will learn how to install Tor and configure it in a way that will allow us to make requests with Python to the dark web via Tor's SOCKS.
Tor Network Settings: Going through Tor Network Settings option, you can set your proxy server if you are using. And If Tor is censored in your country, and. An anonymous reader writes "Viewable with Tor installed, search engine To access the darknet, you need to install the TOR browser Our domain TOR. Step 1: To access the deep web, you need to have a Tor browser on your system..Step 2: First, Download Tor..Step 3: After downloading the Tor. The easiest way to use Tor is through its dedicated browser, which is available for Windows, MacOS, and Linux (it can be run from a USB stick if. Best VPN When Using Tor To Access The Dark Web. Though there are several ways to accessing the dark web, Tor is the most widely used method. Other. On Android Download the Tor Browser app from here Open Tor Browser Click Connect Once a connection is established, you should see an onion. Download and install the Tor browser from their official website. The browser is available in versions that are compatible with Mac, Windows. The Tor browser provides access to.onion websites, which are Tor hidden services that you can only access through the Tor browser.
Brick Market
We supply at affordable wholesale with safety and flexibility in delivery at various location. The market is the oldest dark market currently in existence, having been operating continuously since November 2013. However, it’s what happens next that gives me butterflies whenever my phone beeps. Key Marketing Points: -Amazon bestseller -Author is a contributor at the Huffington Post -Author's concepts are taught at universities worldwide -Author's debut book -Local author events and interviews -National radio campaign -Social media promotion -Author's Web site: 2hourjobsearch. The defendants are presumed innocent until proven guilty beyond a reasonable doubt in a court of law. At the time of this writing, Monopoly has a somewhat limited number of listings. Hyperledger has received considerable contributions from large-scale global enterprises such as IBM, Intel, and JP Morgan to support the collaborative development and ongoing research of distributed ledger technology and blockchain. In practice, this involves one or more trusted parties digitally signing a digital document or decentralized ledger in order to certify that a particular cryptographic key belongs to a particular user or device. The data and subsequent analysis will also help identify new trends, support research and advise prevention activities. Once you make an account, they provide you a wallet where you have to deposit the money before you make a purchase. In 2016, a Turkish citizen hacked the Turkish government’s ID system and downloaded the national ID, name, address, how to access the dark web through tor date of birth and mother and father’s name of 49. To economize on bandwidth, dark market the download ignored all images and only downloaded the text of web pages.

